- Abstract
This paper will explore the current digital war in the United States, a land constantly under siege by foreign campaign influences, social engineering attacks, social media poisoning, and common cybercrime such as phishing, malware, brute-force, virus, and DoS attacks. To expand on the topic, this paper will aim to prove that digital warfare is not a science fiction idea but a currently hidden conflict that has nations constantly under attack, whether publicized or not. The desire to bring to light the possible targets of nation-state cybercriminals and groups, and more importantly, convince the leaders in the government of the necessity to devote time and resources to the U.S.’s cyber defenses is paramount for the U.S. to continue to strive in the world of tomorrow.
- Introduction
In a world filled with misinformation, buried facts, continuous military conflict, ravaging diseases, subpar leadership, and cooperation-owned media, the journey to finding truths is getting more challenging every day. The population of the United States is fed lies and coverups daily, regurgitating stories from one media outlet to the next, all in the effort to deter individuals from gaining a firm grasp on one harsh reality- the world in constant turmoil and the technology that it holds so close to its heart is the double-edged sword of progress. While many scholars, politicians, and those in the cybersecurity field will preach until they run out of breath that the U.S.’s cyberwar is merely a science fiction idea, the fact of the matter is this notion is not only false but all efforts to fight the ongoing battle to secure the United States is directly affected by this incorrect concept.
Every day, the consumption of technology increases in complexity and acceptance. For example, power grids are automated, banking data is warehoused on servers, and militaries and governments depend on their communication strength in the electronic communications network. Not long ago, the greatest means to attack a country was by deploying troops or executing airstrikes; however, since most of everything that can exist on the Internet, is, this is a domain where one can assault at the core of an adversary from opposite sides of the Earth, regularly triggering significantly more damage than a physical assault.
Physical assaults are nothing new in the military, easily identifiable attacks that can quickly be detected and the perpetrator unearthed. In fact, military operations are so prevalent that the facts and figures of their disastrous consequences barely impact everyday citizens. In the civilian world, any form of attack seems to be blown out of proportion- a shooting of two men quickly turns into a mass shooting. A singular instance of a lone individual attempting to blow something up expands, due to the media, into a global terrorist cell with the goal of stealing children. Due to the manner in which the media, and those who cling to its every word, perceive military action compared to civilian events, it makes sense that the general public would be so blind to what was really going on in the shadows of the Internet regarding the never-discussed cyberwar.
- Current Known Cyberthreats
Coordinated and intelligent cyber-attacks can be quite destructive, and the world has only heard of a small portion of the truth. With news involving voting fraud, records of hackers obtaining entry to voting booth terminals, and the magnitude of Russian interference in the past U.S. presidential election, one of the American government’s most vital facets, voting, seems to be under siege from all fronts. It does not matter what one believes in or what their political ideals are; the capability to manipulate and influence a country’s election is remarkably effortless.
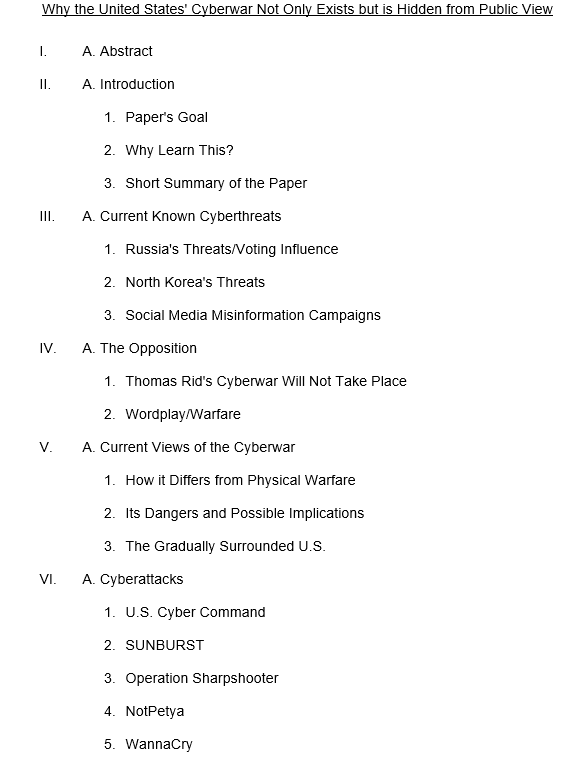
The action of manipulating an election may not seem like a direct act of war; however, in the bigger picture, the ability to select, support, and affect the minds of millions of voters to elect someone who may pose a lesser threat or can be more easily controlled would, undoubtedly, allow their countries to get away with more, and if a physical confrontation took place, will enable the country who is interfering with the election to be victorious. According to the Pew Research Center, the following survey, Figure 1, shows the confidence the U.S. population has in its government to protect its voting systems from hacking and other threats.
Figure 1
Percentage of U.S. Population’s Confidence in Voter System Cybersecurity
Note. Pew Research Center. (2020, August 18). Only about half of Americans are confident the federal government is MAKING ‘serious efforts’ to PROTECT election systems from hacking and other threats. https://www.pewresearch.org/fact-tank/2020/08/18/75-of-americans-say-its-likely-that-russia-or-other-governments-will-try-to-influence-2020-election/ft_2020-08-18_foreignthreats_03/.
Propaganda has been exercised during the path of history by countries all over the globe. North Korea’s efforts to sway its citizens’ minds are among the most notable cases of the effect of social engineering attacks. Since the overall populace of North Korea has limited access to the Internet or any means of communication from the outside world, their government can impose and propagate misinformation on a colossal scale and with tremendous efficiency.
North Korea’s military and cyber forces consist of the leading financial spend of the country’s resources, triggering its citizens to regularly fend for themselves without accessible access to food and water. Regarding North Korea’s involvement in the U.S.’s cyberwar, CNN stated that “North Korea’s army of hackers stole hundreds of millions of dollars throughout much of 2020 to fund the country’s nuclear and ballistic missile programs in violation of international law, according to a confidential United Nations report” (Roth, Berlinger, 2021). The fact that North Korea seems to be constantly in the state of preparing for war on both the physical and digital front, now, more than ever, does the U.S. need to respond accordingly.
DuBois from the Brookings Institution states that “The South Korean government estimates that North Korea’s Reconnaissance General Bureau has dedicated more than 6,000 full-time cyber operatives and support staff who launch disinformation, cybercrime, and espionage operations on a daily basis” (DuBois, 2020). South Korea has engaged in numerous actions to help protect their republic’s infrastructure, ranging from peer-to-peer education, a government-organized data-sharing system, using a structured command-and-control system to answer cyber threats, and robust network separation policies. The U.S. has played a substantial role in assisting South Korea with increasing cyber threat concerns, yet North Korea poses its own unique threats aimed directly at Western Civilization. One of the most crucial factors to North Korea’s triumph in cyberspace is purely its capability to traverse policies and laws that other countries, such as the U.S., adhere to and use to its advantage. North Korea has never been one to blindly follow the rules set forth by the United Nations and its neighbors, performing illegal missile testing, abandoning sanctions, and deceptively acquiring digital resources to finance their military’s constantly growing military strength.
The relationship between North Korea and the U.S. is similar to North Korea bringing a gun to a knife fight. Fighting someone who does not obey the rules leaves those who do severely disadvantaged. North Korea, if remained unchecked, will ultimately have the capacity to slow or stop the U.S.’s progress in many industries, pose (or execute) a significant physical threat, and dominate the digital battlefield. The U.S., blindly following years-old sanctions, laws, and policies, and listening to its non-technically inclined leaders are merely not up to the task of taking on such an emerging threat; this is even more so due to North Korea’s many discussions and often-cooperative actions with the U.S.’s many enemy countries.
With the opening of the Internet, propaganda has the ideal means to distribute hatred, counterfeit news, and other methods of communication utilized to control others. By studying a country’s political viewpoints, what is prevalent with their youth, and obtaining basic knowledge of psychology, another nation can produce false incidents, circulate misinformation to impact elections, control votes, and trigger corporate disarray. The truth of cyberwarfare is that it exists; this idea is no longer science fiction, and any attempts to undermine those who try to disprove this actuality is only preventing those responsible for defending the U.S.’s digital borders from accomplishing their objectives.
- The Opposition
In Thomas Rid’s Cyberwar Will Not Take Place, the author provides an often-shared observation into the validity of the truth of cyberwarfare, “Cyberwar has never happened in the past, it does not occur in the present, and it is highly unlikely that it will disturb our future” (Rid, 2013); this accusation is derived from the definition of an act of warfare, in that its original goal is to inflict physical harm to a person. In Rid’s opinion, if a target such as a Russian power plant were hacked, forced to run outside of normal operating limits, and thus, went offline, the act would not be necessarily an act of warfare. Even if the power plant, as it went offline, caused an explosion that killed all personnel within the facility, it still would not necessarily be considered an act of (cyber)warfare as the original hack was not intended to kill anyone at all; its unfortunate action of murder is merely a side effect.
The thought process of applying wordplay to acts of warfare is, without a doubt, contrary to the goal of clearly accepting that cyberwars exist and will continue to exist. The question to ask is what does denying that any acts of cyberwarfare have existed or will exist do for the security of the U.S? Cyberwarfare’s opinion regarding scholars rivals that of climate change in the past; it is denied, those who support it are ridiculed, and eventually, funding for increasing the security of the U.S.’s cyber defenses is limited to merely satisfy those in power, and those without.
Like the multiple years of climate change denial, the facts of the matter eventually come to light; however, as everyone on the planet is just realizing, this happens too late to make any real change. Instead of waiting for the increasing severity of the weather and the rising sea levels to place enough fear in the hearts of the world’s leaders to convince them that climate change is real, it will take a similar disaster to prove why cyberwarfare is a threat worth taking seriously; this does not have to be the only method for producing results.
- Current Views of the Cyberwar
Due to modern-day society’s dependence on computer systems to operate everything from missile defense systems to transport networks, disrupting a country’s cyber capabilities can influence practically all they do. Unlike conventional military attacks, a cyber-attack can be initiated from any distance, requiring little funding, and having the power to do so incognito. Furthermore, for the most part, wars are begun due to another country’s resources. Oil, the holy grail conquest of the United States, has been the highest motivator in past years. If one country seeks the resources of another, a physical attack with ground troops, air raids, or even a nuclear strike dangers those desired assets. By using a cyber-attack or even, for example, detonating an atomic bomb in the atmosphere over a country to trigger an EMP, one can interrupt or shut down the infrastructure while conserving their precious resources.
In the news, one often hears about cyber-attacks and hacks involving significant damage, and the frightening thing is that with the majority of these attacks, those accountable almost certainly had insufficient financing and human resources. Now, suppose these hackers had millions of dollars, a sizeable team, and the backing of a government; this is what cyberwarfare looks like. Per John M. Donnelly and Gopal Ratnam of S&P Global Market Intelligence’s article, “U.S. is woefully unprepared for cyber-warfare,”a unique view of the U.S.’s cyberwar is provided using an ancient Chinese strategy game, Go; this game was played by those in the U.S. Navy who were examining the country’s cybersecurity status and were led by an outside consultant who offered that playing the game would demonstrate how the U.S. is gradually becoming a target. During the game, two players place and move black and white discs, one by one, on a grid with the goal of encircling the other player’s discs; this game of Go demonstrated how the U.S.’s enemies are playing the long game of encircling and exploiting its weak spots, rather than directly engaging in physical combat. While Go is similar to checkers or chess, it differs by not directly attacking their opponent’s pieces, yet the strategy is equally effective (Ratnam; Donnelly, 2019).
Engaging in an all-out war with an opponent may be standard procedure in the past, but with modern technological advances like the Internet, the world sees new attack methods and vectors that the U.S., and the rest of the world, barely comprehend. Late Alaska Senator, Ted Stevens, famously defined cyberspace in 2006 during a congressional hearing as, “It’s not a truck. It’s a series of tubes” (Singer; Friedman, 2014); this explanation, while humorously inaccurate, does provide one fact- the definition of cyberspace is not widely known, and is even less understood.
- Cyberattacks
The U.S. military’s Cyber Command effectively gathers all cybersecurity organizations, such as the Army’s Ninth Signal Command and the Navy’s Tenth Fleet, and unifies them into a collective with the goal of defending U.S. cyberspace. Cyber Command, while filled to the brim with some of the nation’s top minds, is still ineffective in the U.S.’s cyberwar as two things govern it, politics and finances. A recent well-known failure of the U.S.’s cybersecurity capabilities was the SolarWinds Orion breach.
Also called SUNBURST, the SolarWinds breach has achieved global recognition as numerous organizations involving many government facilities employed SolarWinds’ security services. The hack explicitly targeted a network management product, Orion, and was executed by hackers employed by the Russian SVR. The hack comprised of a maliciously modified update sent through a backdoor in the system. Due to numerous security concerns, including the reality that one of Orion’s update servers was guarded with the password “solarwinds123,” the hack was highly effective and led to organizations struggling to secure their networks and systems (Schneier, 2020).
The threat timeline for SUNBURST commenced on September 4, 2019, when an unauthorized user gained access to SolarWinds. On February 20, 2020, the SUNBURST was implemented, yet it took until December 14, 2020, for SolarWinds to reveal the attack’s information to the SEC. Presently, there are several investigations into the hackers and those involved in the attack by both the White House and international organizations (Panettieri, 2021). The SUNBURST cyberattack could have been averted utilizing a number of security methods, controls, and just basic common sense.
Orion was not open source, thus reducing the number of eyes on the software, restricting the capabilities to detect the threat via auditing to only the corporation’s developers. Also, comprehensive threat analysis of the Orion software should have been completed to precisely pinpoint vulnerable regions in their defensive layers. As an unauthorized user accessed Orion, improved authentication protocols such as 2FA or MFA should have been employed, as well as considerable password complexity requirements. If Orion security staff and developers were proficiently checking access and audit logs, the hack would have been discovered instantly, lessening the time it took for Orion staff to remedy the error. The above security controls would further improve the security of the Orion software, decreasing the odds that a cyberattack, such as SUNBURST, would take place. Furthermore, the security controls would expand the incident response team’s capabilities to swiftly discover and rectify any uncovered security concerns with the software, leading the disaster to develop to such a colossal status as it is presently.
America has been in a cyberwar for many years, and truthfully, it is far from being the victor. Cyberwarfare, identified as the usage of digital strikes to disturb the essential computer networks and systems of a nation, is the latest avenue of existing and potential conflict. A worldwide attack focused on financial, defense, energy, and nuclear companies have been uncovered in recent news. Dubbed ‘Operation Sharpshooter,’ a cluster of hackers targeted critical infrastructure using an innovative social engineering and malware attack.
Not too long ago, former President Trump signed an executive order to enhance cybersecurity in the United States; while this directive was established abruptly following the news of Russian interference in the election, its prospective advantages are considerably more than merely safeguarding voting procedures. Grand View Research shares a graph, Figure 2, of the future U.S. cyberwarfare market by application in the following image; while this provides some assurance that the U.S. might eventually take the threat of cyberwar seriously, this notion can be quickly diminished due to much of the population’s inaccurate views of the potential dangers in the realm of cyberspace.
Figure 2
U.S. Cyberwarfare Market, by Application, 2014-2025 (USD Billion)
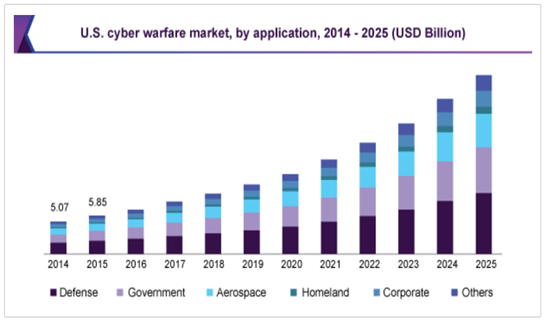
Note. Grand View Research. (2018, February). Cyberwarfare market size; SHARE: Global Industry Report, 2018-2025. https://www.grandviewresearch.com/industry-analysis/cyber-warfare-market.
Mainly used as a technique to unsettle consumers, organizations, and businesses, ransomware can be employed in targeted attacks to destroy data or corrupt data. According to the White House, in the NotPetya ransomware outburst in mid-2018, the U.K., U.S., and other regimes criticized Russia for one of the most devastating and expensive cyber-attacks on record. Although it seemed that the NotPetya attack was aimed initially at Ukraine, similar to a communicable disease, it persisted in spreading throughout the world.
Zero-day vulnerabilities, characterized as flaws, errors, and bugs in code that have not been detected and corrected yet, can be extremely hazardous in the wrong hands; these zero-day attacks are frequently believed to be hoarded for later use or to be merged with other types of strikes. The WannaCry ransomware attack in 2017 was so potent due to a zero-day vulnerability that boosted its effectiveness (which was stockpiled by the NSA); after this vulnerability was leaked to the public, other hackers utilized and altered it, thus improving its success. Stuxnet, a computer worm that pursues industrial control systems, was believed by many to be the first cyber weapon. Formed by the U.S. and Israel to target the Iranian nuclear program, the worm ravaged the systems that operated the centrifuges in their uranium enrichment project; this case hindered the project, thus reducing the progress of Iran’s nuclear capabilities.
Throughout modern-day history, from the Sony Pictures hack in 2014, the DDoS attacks on Estonia, to Ukraine’s power supply disruption using the renowned Trojan, Black Energy, one thing is constant with these events, the escalating fear of cybersecurity. As additional incidents, cyber espionage situations, and new vulnerabilities are uncovered, nations are desperately making attempts to expand their cybersecurity and cyber deterrence. The times of jeopardizing a human life by delivering them to a conflict are over; now, the warriors will undeniably be the geeks in their parent’s basements, with the support of governmental, organizational, or political funding. Stratfor Worldview provides the following timeline, Figure 3, of notable cyber actions.
Figure 3
Timeline of Notable Cyber Actions and Related Dates

Note. Stratfor. (2019, July 5). The U.S. unleashes Its Cyberweapons. https://worldview.stratfor.com/article/us-unleashes-its-cyberweapons-iran-russia-china-cyberwar.
- Why the Truth is not Known
One might ask themselves why the U.S. government would conceal such disastrous events in cyberspace, and the truth is actually quite simple. The general public holds several often-false ideas close to their hearts, the world is at peace, the climate is not getting worse, and tomorrow will be better than today; however, for those who perform their own research in the quest for obtaining knowledge outside of what is fed to everyone by the media, they may understand that there is much more than what meets the eye.
Throughout history, the world has seen countless events that have transpired that affected the public in such a manner that only strengthens the elite’s choice of withholding specific facts and figures; this includes terrorist attacks, military operations, and now more than ever with COVID-19. The fact of the matter is that ignorance is bliss concerning the population; a docile, non-informed species is much easier to control than an educated one. While mentioning aliens in such a paper might go against several do’s and don’ts of the educational climate, the parallel comparison between how humans would react to the sudden announcement of extraterrestrials and the realization of the current cyberwar that the U.S. is facing poses some interesting similarities.
Fear alters everyone in one way or another and can have both constructive and adverse outcomes. Everyone from legislators, religious advisors, and sizeable organizations use fear to their benefit. In a realm bursting with immorality, prejudice, and conflict, fear rules and encourages humans to make changes and defend their constitutional rights and privileges. The extensive usage of fear is nothing unfamiliar, and numerous fantastic authors and political figures have defined both the advantages and disadvantages of using it. If administrations and lawmakers use oppression and fear to govern, harmony and success will be tougher to achieve and sustain; to fight against this, every citizen must resist corruption, ill will, obliviousness, and above all, fear.
In America, for example, fear is relatively common; whether it is fear of incarceration, distress, mortality, property, or malfunction, it, as a nation, is ruled by threats of judicial, societal, or visceral punishments. Countless residents of the United States are residing in an always-present state of fear. Fear of global warming, probable wars with North Korea, Russia, or their many other enemies, and COVID-19 are just a few worth mentioning. Fear comes from ignorance, ignorance of what is happening and what might happen; it is very similar to an individual’s fear of opening an unknown door in a dark room- the person is afraid because they do not know what will be behind it. The only way to prevent the spread of political fear is by proper education. The door must be opened to the truth of the cyberwar that currently exists, how it can grow, and how it can be prevented; however, this dream may never be realized due to the U.S.’s inability to change its ways.
Another reason why the truth about the current cyberwar is being hidden is quite apparent, politics. The information superhighway has done more for big business than any technology in the past, connecting billions of customers to the organizations that create what they need or desire. If more of the population were privy to the actuality of the risks on the Internet, sales would go down, more individuals would think twice about clicking “accept” on an application or website’s terms and conditions pop-up, and fear would spread much like the pandemic that is currently ravaging businesses around the globe. Some excellent politicians work for the citizens that placed them into power, and some might as well sell out real estate on their suits for company logos, much like in NASCAR.
Hiding the truth about the immense number of active threats and risks that continuously grow and evolve towards the U.S., many of which are from other countries with less-than-ideal views of the manner in which the U.S. operates, is, quite frankly, a smart move; however, this only applies if it did not directly affect the everyday citizen in a manner that might one day destroy their way of life. Hiding the truth from those one leads can often be a necessary part of management, yet in the case of the U.S.’s cyberwar, this only prevents the country from taking things seriously, leaving the nation unprotected and unaware of the numerous attacks to their infrastructure, voting practices, and information.
- COVID-19
Misinformation campaigns are on the rise as of late, and interestingly enough, internet censorship’s dynamic with it is often confusing. As stated by Vivian Roach of Baylor Lariat, “In the era of the COVID-19 pandemic, an “infodemic” has also emerged” (Roach, 2020). Misinformation has impacted everyone, yet the policies companies like Facebook enacted, such as tagging posts and marking them as ‘going against their community standards,’ directly interferes with the right to free speech, whether wrong or not. Many individuals would suggest combatting misinformation with intense internet policies and regulations; however, should the level of constraint on U.S. citizens regarding internet usage really mirror a country such as China?
Presently, COVID-19 has changed the way organizations conduct business, how they advertise, sell their products, and even how their employees perform their daily duties; this only adds fuel to the fire for cybercrime targeted at the U.S. As INTERPOL states, “Cybercrime has shown a significant target shift from individuals and small businesses to major corporations, governments, and critical infrastructure” (INTERPOL, n.d.). Due to countless personnel who are working from home and the abruptness of the transformation, organizations are desperately struggling to safeguard the remote systems and networks they install and manage, thus permitting cybercriminals to benefit from the often-frail defensive measures and the readiness of work-from-home employees to click on malicious links in emails that they would consider as required to accomplish their occupation’s obligations.
The expression, ‘when it rains, it pours’ is, regrettably, appropriate for this pandemic, as financial, social, and political turbulence produces a rapid increase in the armies of the wicked, endeavoring to gather data, harm industries, and steal possessions in their cyberattacks against those who are already in a state of turmoil. Per one of INTERPOL’s private sector partners, from January to April in 2020, a total of 909,000 spam messages, 48,000 malicious URLs, and 737 malware incidents were reported, all related to COVID-19 (INTERPOL, n.d.). With the inadequate technological familiarity of leaders, their incapability to work with each other in sharing ideas and establishing cyber norms, as well as the absence of cybercrime policies and punishments in several countries, the rise in cybercrime aimed at the U.S. will do nothing but rise as COVID-19 will not be the end of the dangers to come. Microsoft provides the following look at the beginning months of 2020’s battle with COVID-19 and its effects on cybersecurity in Figure 4.
Figure 4
Trend of COVID-19 themed attacks

Note. Microsoft. (2020, September 17). Exploiting a crisis: How cybercriminals behaved during the outbreak. https://www.microsoft.com/security/blog/2020/06/16/exploiting-a-crisis-how-cybercriminals-behaved-during-the-outbreak/.
- What is Needed to Spread the Truth About/Fight the Digital War the U.S. is Facing
An effective method to demonstrate the importance of educating the U.S.’s population and leaders on the rising dangers from the cyberwar it is facing is to take a quick look at how the tragic events on 9-11 impacted security in the nation as a whole. Armed with simple boxcutters, terrorists were able to successfully penetrate defenses and land a blow so massive that the world changed; these boxcutters would often be considered as not a risk, similar to how the U.S. currently views Russia’s involvement with its voting processes and China’s numerous attacks on the U.S.’s infrastructure and its organizations. A weapon that is not feared can often inflict the most dramatic wounds.
After 9/11, the U.S. intelligence program grew in financial support, complexity, and use. The Patriot Act was one of the most significant programs introduced, expanding the U.S. government’s capability to use technology-based detection and recording systems. In addition, by eliminating much of the ‘red tape’ that encircled the U.S.’s debatable surveillance systems, it was permitted to turn their awareness from break-fixes to thwarting future terrorist attacks, thus revolutionizing its security tactics and turned their protective measures from acting reactively to preemptively. While 9/11 certainly was a horrible event, much like COVID-19, there are silver linings. For the first time, the U.S. thought as one and took outside threats seriously, yet now, it faces dangers from foreign countries armed with a lot more than boxcutters, and their weapons are hidden by politicians and military leaders.
There are several methods of improving both the U.S.’s defensive and offensive capabilities in its current global cyberwar. First and foremost, while this should not even be an issue, the truth of the cyberwar needs to be realized by all; its current threats and possible future implications need to be understood by everyone, so more funding is allocated, and more skilled professionals are trained in cybersecurity. Next, U.S. leaders, generally comprised of older white gentlemen with no accurate understanding of even the basics of the Internet, need to train in technology to a point where they can understand the general correlation between the devices the U.S. uses and their impact on the cybersecurity of the nation.
While merely replacing much of congress with younger tech-savvy individuals would be ideal, this hope is obviously not obtainable as of yet; at the minimum, these leaders who have led the U.S. for decades need to learn from their advisors and peers, aiming to devote both time and resources to those who are defending the country’s digital realm. It is true that swaying the minds of most leaders can be quite complicated, especially over something such as climate change, where for so long, everyone thought it was a hoax, much like the current cyberwar the U.S. is involved in; however, one thing that politicians understand is finances, so the argument should be built using scenarios such as a cyberattack on the U.S.’s banking system, theoretically crashing the stock markets and dwindling politicians’ precious digital wallets.
Similar to any battle fought by the U.S. in its generations of conflicts around the globe, there are weapons in the digital war it is facing now that they will need to utilize; many of these are quite different from the typical bullet or missile that the nation has come to love, yet when applied correctly, can have much more effectiveness at defending the country’s digital assets. A comprehensive and thorough re-education campaign targeting both voters and their representatives needs to be performed regarding the U.S.’s cyberthreats, how it affects the everyday citizen, and what can be done to prevent them from occurring.
Next, cyber norms, definitions, and best practices need to be clearly designed, taught, and discussed with cybersecurity departments worldwide; as of now, much of cyberspace regarding policies, laws, and regulations often feels like the wild west, a lawless realm of chaos without even the necessary framework of authority to apply the firm grasp of righteousness. Much like project management, communication is essential when planning a war; since this specific war exists online, not utilizing the information superhighway to undermine cybercriminals’ efforts is simply strange, yet that is currently happening.
- Summary
The U.S. is facing a rising behemoth in the form of a digital war; this battle can make all previous physical confrontations look like mere schoolyard disagreements over lunch money. What makes the U.S.’s cyberwar so dangerous is the fact that many do not even know that it exists due to lack of worldwide and inter-departmental communication, misidentification of the various threats and attacks that have already occurred, and how ill-prepared the U.S. is in regard to its current security measures and lack of funding.
The world’s superpowers are steadily increasing their digital armies and marking their targets for future assaults, while much of the U.S. is still seemingly debating the authenticity of COVID-19 or arguing about the shape of the planet. The truth and the gravity of the U.S. cyberwar need to finally be accepted by the nation’s leaders and those that vote them into power before it is too late. If the U.S. follows its standard operating procedure of only making changes once they are forced to, similar to its response to global warming or COVID-19, the future of the nation will be uncertain as China, Russia, and North Korea are the sharks in the water slowly encircling its prey- the obese, ignorant child frantically flapping his arms around while believing he is drowning, not realizing he is only in a few inches of water.
Annotated Bibliography
C.B. Insights. (2020, October 29). Weaponization of the future: Digital warfare & disinformation: C.B. insights. Retrieved June 1, 2021, from https://www.cbinsights.com/research/future-of-information-warfare/.
In this article, disinformation’s use in the digital battlefield is investigated, focusing on the U.S. and several other countries’ battles with COVID-19 and misinformation campaigns. By spreading false information on a rival country, the attacker can slowly influence their population into believing what they want them to. This article explores the future of information warfare, emphasizing reconnaissance, weaponization, attacks, infections, and their impacts. As words are far less threatening and noticeable compared to, say, a missile attack, this information is of great help to the cause of convincing the nation that it must devote time and resources to defending against the threats it is facing on the digital battlefield. The publication also discusses deepfakes, automated phishing attacks, computerized propaganda, social media, and the many methods one can implement to defend the U.S. from cyber threats.
DuBois, E. (2020, December 23). Building resilience to the North Korean Cyber threat: Experts discuss. Retrieved June 1, 2021, from https://www.brookings.edu/blog/order-from-chaos/2020/12/23/building-resilience-to-the-north-korean-cyber-threat-experts-discuss/.
This article explores the cyberthreats of North Korea and how they can/will impact both the U.S. and South Korea; this information is derived from the Asia Transnational Threats Forum in October of 2020, which held a virtual roundtable on cybersecurity focused primarily on North Korea. The article shares information about the current policies that the U.S. is utilizing in its defenses, future solutions to the emerging threats of North Korea’s aggressive nature, and opens discussion for future worldwide forums to figure out how the U.S. can improve its cybersecurity policies and protective measures.
Grand View Research. (2018, February). Cyberwarfare market size; SHARE: Global Industry Report, 2018-2025. Retrieved June 1, 2021, from https://www.grandviewresearch.com/industry-analysis/cyber-warfare-market.
This article shares data on the U.S. cyberwarfare market and how it has grown in recent years; its increase in funding shows how the cyberwar both exists and is quickly increasing in its ability to bring much of the world to its knees. While the growing funding for the U.S.’s cybersecurity market shows that there is still room to grow as more cyberattacks occur seemingly every day. One would think that with the increased funding for the U.S.’s cybersecurity capabilities, one would not have to argue the actuality of the cyberwar that it is currently in; however, many scholars constantly try to disprove its existence.
INTERPOL. (n.d.). INTERPOL report shows alarming rate of cyberattacks during COVID-19. Retrieved June 1, 2021, from https://www.interpol.int/en/News-and-Events/News/2020/INTERPOL-report-shows-alarming-rate-of-cyberattacks-during-COVID-19.
This article shares many facts and figures about the current state of COVID-19’s impact on much of the world regarding cybersecurity; this includes increases in cyberattacks such as online scams and phishing, disruptive malware (ransomware and DDoS), data harvesting malware, malicious domains, and misinformation campaigns. Many countries are utilizing the often-weak security of U.S. business to create targeted attacks utilizing scare tactics involving COVID-19; its implications on a larger scale should strike fear into the hearts of U.S. leaders concerning the country’s cyber defenses.
Libicki MC. Cyberdeterrence and Cyberwar. RAND; 2009. Retrieved June 1, 2021, from https://search-ebscohost-com.ezproxy.bellevue.edu/login.aspx?direct=true&db=cat04787a&AN=belle.1917174&site=eds-live.
This book discusses cyberspace’s value in worldwide economic and military power and solidifies arguments on how the U.S.’s digital cyberwar is currently occurring with no signs of slowing down. The author continues by exploring cyberspace’s current laws and policies, threats, types of attacks, and reasons why the U.S. is vulnerable to a wide range of potential dangers. The most important aspect of this book is how exactly the U.S. can protect itself; this is the primary purpose of this paper after proving that the U.S. is currently at war in the digital world, a battle that will continue to rage on unless it makes significant changes to leader’s perception of often-intangible threats and assets.
Microsoft. (2020, September 17). Exploiting a crisis: How cybercriminals behaved during the outbreak. Retrieved June 1, 2021, from https://www.microsoft.com/security/blog/2020/06/16/exploiting-a-crisis-how-cybercriminals-behaved-during-the-outbreak/.
This article explores how COVID-19 has impacted cybersecurity by growing the number of cyberattacks, phishing attempts, and other illegal actions in the digital landscape; this increase is worrisome due to the massive and sudden switch of many organization’s employees to work from home status, as well as the increased likelihood of clicking on malicious files due to using descriptions and email titles involving COVID-19 and the U.S.’s stimulus payouts. During any war, a virus or disease outbreak can wreak havoc on routine operations and reduce the effectiveness of defensive measures; in the digital war the U.S. is facing, this creates a worst-case scenario.
Panettieri, J. (2021, February 22). SolarWinds Orion Security Breach: CYBERATTACK timeline and hacking INCIDENT DETAILS. Retrieved June 1, 2021, from https://www.channele2e.com/technology/security/solarwinds-orion-breach-hacking-incident-timeline-and-updated-details/.
This article shares the timeline of events of the SolarWinds hack, highlighting the improper security protocols of the affected company (and those who utilized the software), as well as the long time it took for the breach to be identified, reported, and remedied. The timeline allows the reader to see how the typical cyberattack evolves, the inability to defend against them in the U.S. and worldwide, and view the ability of such an attack to cripple many organizations. With an organization such as SolarWinds who sells its products to many government entities, its lack of proper security protocols highlights the necessity for improvement in the U.S.’s cyberdefenses.
Pew Research Center. (2020, August 18). Only about half of Americans are confident the federal government is MAKING ‘serious efforts’ to PROTECT election systems from hacking and other threats. Retrieved June 1, 2021, from https://www.pewresearch.org/fact-tank/2020/08/18/75-of-americans-say-its-likely-that-russia-or-other-governments-will-try-to-influence-2020-election/ft_2020-08-18_foreignthreats_03/.
Pew Research Center’s article shares the current views of the population of Americans who believe that the U.S.’s current cybersecurity abilities are inadequate to protect against its election systems and the country as a whole. By utilizing data and graphs, this information is clearly presented in a manner in which supports the necessity for increased devotion to the U.S.’s defensive capabilities in cyberspace. Since the U.S.’s voting systems have been attacked before by Russia, the fact that so many in the U.S. do not feel that it is still secure is quite interesting yet infuriating at the same time.
Ratnam, G., & Donnelly, J. M. (2019, June 26). U.S. is woefully unprepared for cyber-warfare. Retrieved June 1, 2021, from https://www.spglobal.com/marketintelligence/en/news-insights/latest-news-headlines/us-is-woefully-unprepared-for-cyber-warfare-52560026.
This article discusses how the hidden war on the U.S. is, in fact, hidden, as well as points out the ‘gray zone’ that is cyberwarfare. The article focuses on threats from various countries such as China, North Korea, Russia, and Iran; in addition to this list, terrorist groups are included. An interesting aspect of this publication is the author’s belief that the digital war is not only existing, but Americans are losing the battle that politicians fail to address and fight. The Navy cybersecurity review, which was made public in March of 2019, clearly indicates the many threats both the military and the U.S. face and the ‘defenseless defense’ the nation’s politicians seem to support.
Rid, Thomas. 2013. Cyberwar Will Not Take Place. Oxford University Press, Inc., USA.
This book shares the opposition’s view to the argument that the U.S. is currently in the midst of a cyberwar; the author states that it does not and will not ever exist due to primarily the definitions of what an actual act of war is, and how cyberattacks in the past were primarily just attempts to damage or steal assets and resources. The author also shares the history of cyberattacks, current events, and what he predicts is the future of cyberwarfare-style attacks. The information in this book will help create a baseline between the arguments in this paper and provide the necessary data on how cyberwar not only exists but is an always-increasing threat.
Roach, V. (2020, October 02). Censoring fake news on social media presents a slippery slope. Retrieved June 1, 2021, from https://baylorlariat.com/2020/10/02/censoring-fake-news-on-social-media-presents-a-slippery-slope/.
This article explores the relationship between the “infodemic” and internet censorship; the correlation between the two offers a unique perspective into the potential dangers of misinformation campaigns used in cyberwarfare and cyberattacks. With the sudden rise of work-from-home employees, scare tactics, and fear-driven phishing attacks, COVID-19’s impact on cybersecurity has changed the entire world, thus creating new areas of entry for cybercriminals and nation-state hacking groups.
Roth, R., Berlinger, J. (2021, February 09). North Korean hackers stole more than $300 million to pay for nuclear weapons, Says Confidential U.N. report. Retrieved June 1, 2021, from https://www.cnn.com/2021/02/08/asia/north-korea-united-nations-report-intl-hnk/index.html.
This article shares how North Korea is funding its military and cyberwarfare capabilities by often shady methods. North Korea has always been known for its aggressive stance towards the U.S., as well as its advanced and extensive hacker groups. North Korea relies on income generated by hacks and mining cryptocurrencies for such a country with less-than-ideal relationships with possible trading partners. As North Korea is one of the U.S.’s most significant cyberthreats, this article will show how they fund their offensive abilities and why the U.S. must devote more time and resources to their defensive abilities.
Schneier, B. (2020, December 23). The U.S. has suffered a MASSIVE Cyberbreach. It’s hard to overstate how bad it is | Bruce Schneier. Retrieved June 1, 2021, from https://www.theguardian.com/commentisfree/2020/dec/23/cyber-attack-us-security-protocols.
This article discusses the SolarWinds breach in its entirety, sharing helpful information into one of the largest hacks for quite some time. While the attack was worldwide, the U.S. utilized Orion, the network management product that an unauthorized individual/group accessed as accessed by several large U.S. organizations and even some government agencies. The SolarWinds hack was an unfortunate wake-up call for the U.S. and shares a glimpse into the possible ramifications of the future of cyberwarfare.
Shostack, A. (2014). Threat modeling: Designing for security. Indianapolis, IN. Wiley.
This book will provide the basics of threat modeling, a process that will assist this research by finding the problem areas in the U.S.’s national security, deciphering how other countries are exploiting these weaknesses, and figuring out how to defend against the digital war it is currently in. Shostack’s book explores what threats are, how to find them, why they exist, and what can be done with them, emphasizing software development. While this paper will focus on the often hidden cyberattacks the U.S. faces, such as election meddling and misinformation campaigns, the information in this book immensely valuable in shedding light on the underground digital war and putting ideas into terms other cybersecurity professionals and the common citizen will understand.
Singer, P. W.; Friedman, Allan. Cybersecurity and Cyberwar: What Everyone Needs to Know, Oxford University Press, Incorporated, 2014. ProQuest Ebook Central. Retrieved June 1, 2021, from https://ebookcentral.proquest.com/lib/bellevue-ebooks/detail.action?docID=1538365.
This book explores the various pressing issues in cybersecurity and utilizes simple terms that will help create this paper in a manner fit for any reader’s skill level. Topics addressed in the book include hacktivism, patriotic hackers, attacks such as Stuxnet, and Iran, China, Israel, and Russia’s threats against the U.S. The authors take a unique look at assessing why threat assessment in cyberspace is so tricky, how the current cyberwar can either equalize or diffuse power, and discusses cyber norms and trends now and into the future.
Stratfor. (2019, July 5). The U.S. unleashes Its Cyberweapons. Retrieved June 1, 2021, from https://worldview.stratfor.com/article/us-unleashes-its-cyberweapons-iran-russia-china-cyberwar.
This article shares how former President Trump signed a directive that changed the often-non-aggressive stance of the U.S. concerning its cyber capabilities; however, depending on how one views this former President, one can assume that this action is widely just based on words. The article also shares a timeline of notable cyber actions, their descriptions, and their dates; this information explores how cyberwarfare has existed for many years, and despite the U.S.’s “best” efforts, the fight is long from over.
Categories: Security







1 reply »