
Summary
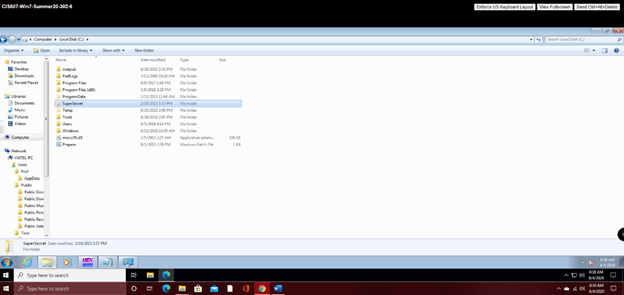
In this scenario, we are investigating an employee at our company for misusing company property by stealing other employee’s identities and running a side business. The first thing I attempted to do once I logged into the Sandbox VM was to try to access the suspect’s account with the username of “Anybody;” this account’s password was not able to be guessed, and the password hint did not work. Next, I decided to see what I could do with the account I did have access to, the “Toor” account. After searching through all the data with no success, I wondered if there were any hidden folders on the C:/ drive. So, I selected the Start button, then Control Panel > Appearance and Personalization. Next, I selected Folder options, then the View tab. Under Advanced settings, I selected Show hidden files, folders, and drives, and then pressed OK. To my surprise, I located a hidden file named “SuperSecret” that contained a Text Document called “Anybody.”
Once opened, I was presented with another hurdle, attempting to crack the below data in my attempt to get the password.
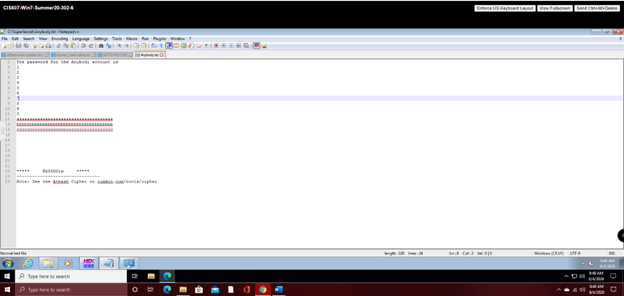
At the bottom of the text file on line 24, I noticed the following note:
“Note: See the Atbash Cipher on rumkin.com/tools/cipher.”
So, I then navigated to that webpage; once I arrived, I selected the Atbash cipher, and was presented the following screen:

Then, I typed in the encoded text from the SuperSecret folder, Kz55D0iW, and was presented the following password after decoding it:
| Pa55W0rd |
Next, I went back to the VMWare environment to try out the password.
Success! After entering the now decrypted password, I was able to get into the system. It turns out that the password hint was actually pretty good. I was notified that the password was old and needed to be remade, so I changed it to a simple one, “Password.”
Now that I am finally into the suspect’s account, I can begin the investigation. I need to find any evidence of the misuse of company computers, identity theft, or running a side-business with the machine.
Here is what I found:
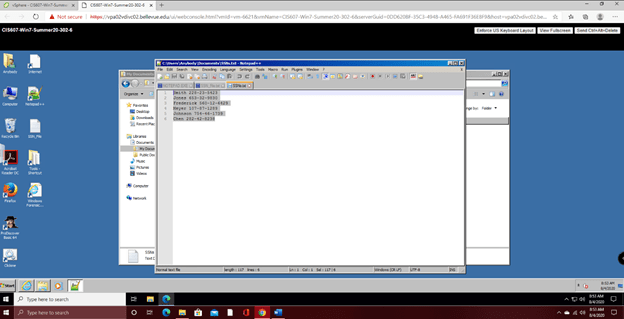
A Notepad++ document containing six names and social security numbers, shown below:
Several potentially dangerous documents, files, and folders with the name of Virus, shown below:

I wanted to figure out if the virus was self-inflected to cover up the suspect’s actions or if he used it to extract the sensitive information from his employees. So, I took a look at when the Virus files were created and found the following data:
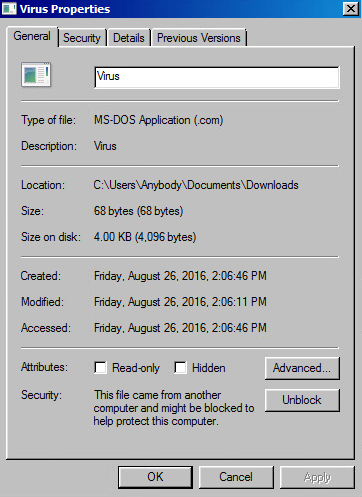
As you can see, the virus files were created on Friday, August 26, 2016.
Next, I took a look at the Clickme program on the desktop, which is what I believe the target opened to download the virus.

As you can see, the Clickme program was created on Monday, December 29, 2014.
Armed with this information, I believe that the target’s PC was indeed infected, as he opened the Clickme program on Monday, December 29, 2014, shown below:

Now, I wanted to figure out if the collection of SSNs and credit card numbers were created due to the virus, or if the suspect was responsible. So, I took a look at when the SSN_file document was created and found the following:
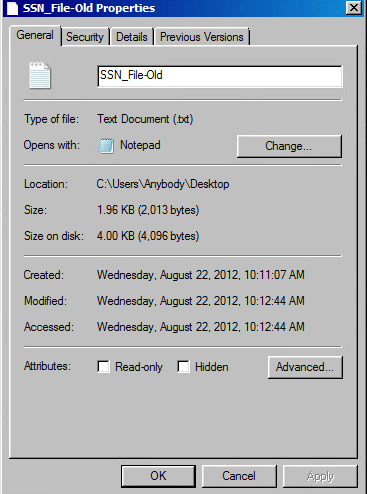
As you can see, the file was created in 2012, far before the virus originated.
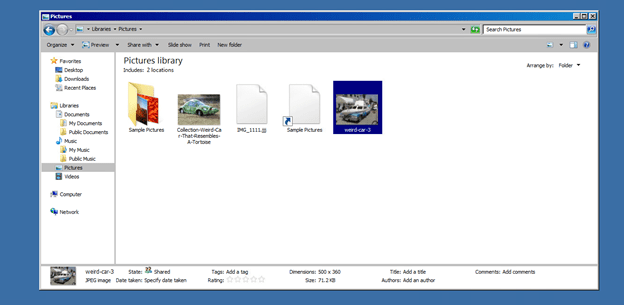
I then found two odd images in his pictures library, so I examined them to see if any hidden data was located in them. I was unable to find anything.
A .txt file named, “SSN_file.txt” that seemingly contained several credit/debit card numbers, shown below:

I also found a similar file named, “SSN-File-Old.txt.” in the users Recycle Bin, shown below:

Next, I decided to go back to the images I found and see if I can find anything else about them. I opened up QuickStego and found the following in the image titled, “a.”
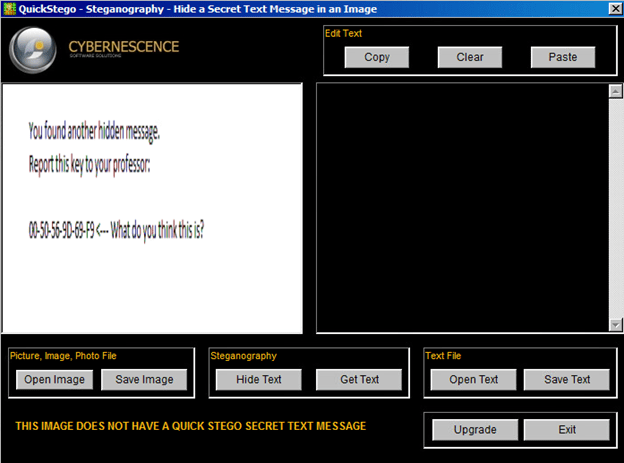
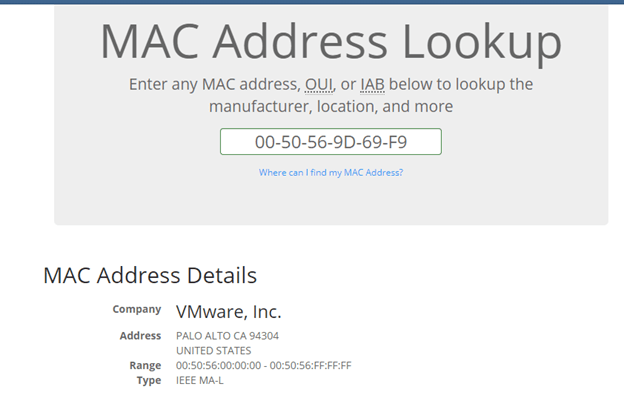
After my first examination of the numbers, I believe they could be a MAC address, so I went to a website that identifies MAC addresses and found the following:
Next, I turned my attention to the Clickme file on the desktop. After trying to figure out how to get into whatever it is by solving the equation, I opened its file location and was greeted with the following message:

After not being able to get any further, I navigated to the temp file in C://.
While there, I found the following:

In Secretfile 1, I opened the image in notepad and found the following:

In Secretfile3, I opened the file with Windows Photo Viewer and found the following image:

I tried to make a copy of the image so I could open it up in Quick Stego, but it did not show up.
Overall, I believe I have found enough incriminatory evidence proving that the suspect was indeed guilty of misusing company property and stealing personal information from his employees. I didn’t, however, find any evidence of the suspect running a side business unless the side business was stealing employees’ identities. I believe the suspect self-inflicted a virus onto his PC to either cover up his wrongdoings or possibly did it due to user error, proving his misuse of company property.
Reference
Nelson, B., Phillips, A., & Steuart, C. (2019). Guide to Computer Forensics and Investigations. Boston, MA: Cengage Learning.
Categories: Security






