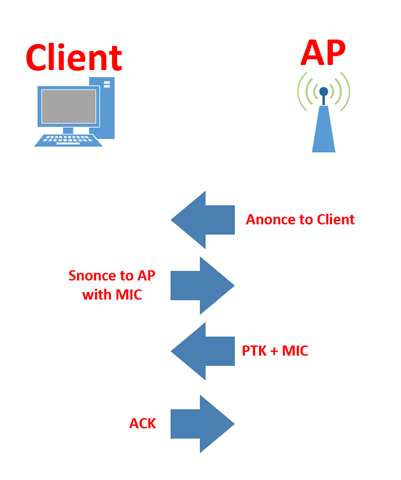
The 4-way handshake is the process of sending and receiving four messages between an authenticator (access point) and the supplicant (client device); this generates encryption keys which are then used to encrypt data sent over wireless connections. There are several different keys used in the 4-way handshake, including the MSK (Master Session Key), PMK (Pairwise Master Key), GMK (Group Master Key), PTK (Pairwise Transit Key), GTK (Group Temporal Key), Anonce, Snonce, and MIC.
The PMK (Pairwise Master Key) is the first step involved in the 4-way handshake once the 802.1x EAP and open system authentication have finished. Next, the access point sends an Anonce or authentication Nonce to the client; once this is received, the client takes the PMK and the client’s AP’s Anonce and creates a PTK (Pairwise Transit Key). Next, the client sends its Nonce (Snonce) to the access point. Now, the AP can process and generate the same PTK (Pairwise Transit Key) as the client, thus encrypting and decrypting data sent between the two access points without ever having to transmit the PTK (Pairwise Transit Key) over the wireless network. Using the RSN (Robust Secure Network) information element, the AP verifies and validates it by sending a frame. Finally, the ACK (acknowledgment) of the EAPol key must be verified as complete. The 4-way WPA2 handshake can be captured using various tools such as Hashcat and Wireshark, and dictionary-style attacks can attempt to crack the keys used in the handshake. The weakness allows an attacker to initiate a man-in-the-middle attack while performing a Key Reinstallation Attack (KRACK) by replaying packets used in the authentication process.
Categories: Networks






