
- Use the nmap (text interface) or zenmap (GUI) tool to map the network (192.168.25.x) your client currently resides on. You should only map the range 192.168.25.1-99. Hosts at 192.168.25.100 and above are student systems and not part of the assignment. We will start with a ping scan to see what systems are active on the network range you have been assigned.
- If using zenmap, once you have started the program type in the Target text box the IP addresses or range of addresses you want to scan. In the Profile box, change it to Ping Scan. Click Scan.
- If using the command line version of nmap the command would be nmap –sn <target ip address range>. Note, you shouldn’t type the ‘<>’ characters. For the ip address range you should use the subnet you are on (in this case remember that is the first three groupings of numbers) and the last grouping should be 1-99. So your completed command would have the form nmap –sn nnn.nnn.nnn.1-99. Remember that for this class we are going to limit your scans to the 1-99 range as all your student machines have ip addresses with host numbers > 99.
- Wait for the results!
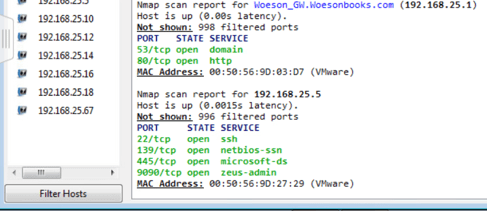
- Take a screen shot of the results and paste it below. The first page of nmap/zenmap results is all you need.

- What did this scan tell you about the hosts on the network? How many, what IP, anything else?
By performing the Zenmap ping scan, I was presented with the following information:
- It showed me the date of the scan, so if I kept performing these scans and checking for what time of the day more systems are on/off, I could better understand their typical work hours and the likelihood of each device to be, for example, a server that is rarely shut off.
- I was also able to see the domain name of the IP address I was provided; in cases where you are only given an IP address, this would help determine the geological location and website’s the target utilizes.
- Next, I could see a list of all online devices and relevant information such as their MAC and IP addresses, as well as the time it took for the scan (searching merely for a range of IP addresses takes less time and is less noticeable than if doing an entire ping.
- The scan you just ran is a ping sweep. It will help you find live hosts but it is also noisy on the network. If it’s important to the test you may decide to only scan for a few hosts at a time or otherwise slow down your scanning so as to be less noticeable.
- After finding active hosts you will want to determine which ports are open. One way to do this is by conducting what is known as a full open or port scan. One problem with a full open scan is it is noisy, you are making actual connections to those systems which will show up in logs along with your ip address. Another option is to run what is known as a SYN, stealth or half-open scan. With this scan the three-way handshake is not completed, thus no connection, thus less to be noticed by observant sys admins. This scan may sometimes not provide as accurate results but you have less chance of having your activities noticed. You can conduct a stealth or half-open scan with the command nmap –sS <target ip address range>. This exact scan is not included in the preset profiles in zenmap.
- Run a SYN scan using nmap (not zenmap) against the active hosts you found with your ping scan. What information does the scan reveal about the hosts on the network? Provide specifics.
The SYN scan was more detailed and generated details on each active host, such as the number of ports scanned and their port state. Ports able to be examined were recorded with their service and port number. Ports that were filtered and could not be scanned were not displayed, only the total number. Additionally, the scan showed the latency of each host, whether the address was IPv4 or IPv6, and their MAC address.
- Run one additional scan of your choosing using either nmap or zenmap. Explain what the scan does and what you found.
The additional scan I ran was the Traceroute scan; this used Nmap and returned whether the host was active, its latency, the number of involved hops, the path to the host, and the MAC addresses of the server and its respective VMware servers.
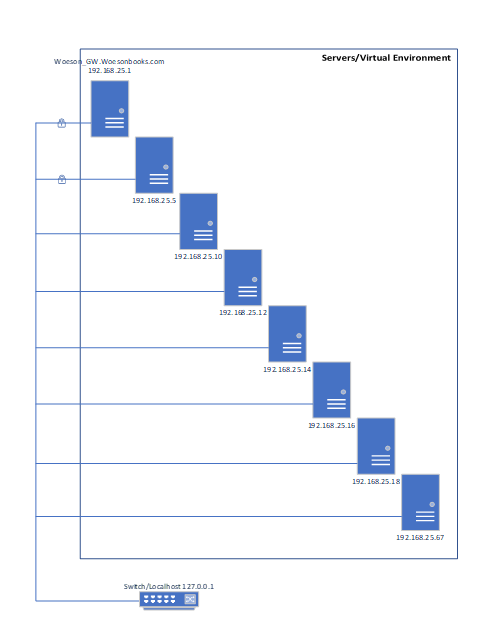
- Using the information you gathered from your scans provide a diagram of what you think the network you are scanning looks like. Provide information such as host IPs, open ports, supported services, anything else you can determine about the network and connected hosts. You can do the diagram in any tool you choose to use. Include a screen capture of the final map. You can use the map drawn by zenmap as part of your research but you should not provide that map as your response to this question.



| Host IP | Open Ports | Supported Services |
| 192.168.25.1 is encrypted | 53, 80 | Domain, HTTP |
| 192.168.25.5 is encrypted | 22, 139, 445, 9090 | SSH, Netbios, MS-DS, Zeus-Admin |
| 192.168.25.10 | 135, 139, 445, 5357, 5666, 49152:53:54:55:56:57 | MSRPC, Netbios-SSN, MS-DS, Wsdapi, NRPE, Unknown |
| 192.168.25.12 | 135, 139, 445, 5666, 49152:53:54:55:56:57 | MSRPC, Netbios-SSN, MS-DS, NRPE, Unknown |
| 192.168.25.14 | 135, 139, 445, 5666, 49152:53:54:55:56:57 | MSRPC, Netbios-SSN, MS-DS, NRPE, Unknown |
| 192.168.25.16 | 135, 139, 445, 5666, 49152:53:54:55:56:57 | MSRPC, Netbios-SSN, MS-DS, NRPE, Unknown |
| 192.168.25.18 | 135, 139, 445, 5666, 49152:53:54:55:56:57 | MSRPC, Netbios-SSN, MS-DS, NRPE, Unknown |
| 192.168.25.67 | 21, 80, 135, 139, 445, 1433, 2383, 5666, 49152:53:54:55:56:57 | FTP, HTTP, MSRPC, Netbios-SSN, MS-DS, MS-SQL-S, MS-OLAP4, NRPE, Unknown |
Categories: Security






