In this week’s assignment, we are tasked with creating a Virtual Machine environment; for my choice, I decided to go with VMware Workstation Player 15. As I had yet to ever utilize Linux outside of a few school assignments many years ago, I am thrilled to have the chance to learn the OS. My first task was to read up on VMware’s products and decide upon a VM service. I decided that VMware Workstation Player 15 would be sufficient in hosting my virtual environment; once I found the latest version, I started the install. For this assignment, I downloaded the VMware Workstation Player version 15.5.6. As I have been preparing to run multiple various operating systems for quite some time, I, thankfully, just upgraded one of my computers with 48GB of RAM.
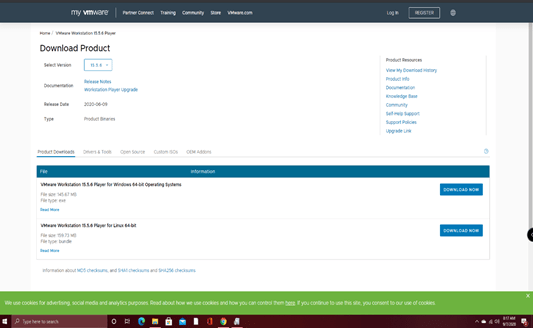
After VMware Workstation Player 15 finished downloading, I began to set up the software.

Next, as I am using VMware Workstation Player 15 for non-commercial use, I was able to bypass the need for a license key.

Then, I was presented with the requirement of locating an Installer Disk Image File (ISO). I have read in the past that Ubuntu is an excellent version of Linux, which is useful for beginners to learn the system.

After deciding upon Ubuntu, I began downloading their ISO file (which took rather long).

After downloading, I selected the Ubuntu ISO from the menu.

After selecting Next, I then was presented with the following screen, requiring me to personalize Linux with my full name, user name, and password.

After entering my data (and saving the information for later), I was then presented the following screen asking me which drive I would like to utilize and to create a name for the VM. As I am running out of room on my SSD (future upgrade), I chose to use my 1TB HDD instead.

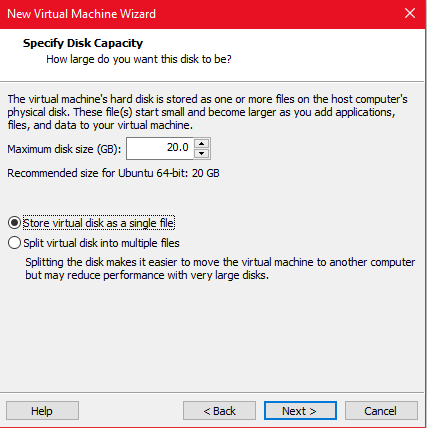
Next, I needed to allocate the disk size for the VM, so I just went with what the software suggested (20GB). As I have no plans to move the VM to another computer, I decided only to store the data in a single file.
Then, I was shown the image below, which merely had me check if all of the settings are correct.

Just as everything was going smoothly, I received the following error message.

After reading the error message, I decided to go into my BIOS settings and check the status of Intel VT-x. While I have no images of the changes I made in the BIOS menu, I enabled Intel VT and turned on a few other VM settings I found. After making the changes, I found success by being able to get into Ubuntu!

I was first presented with an available update, so I went ahead and downloaded it.

After updating, I was presented with the login screen. So, I then chose my already-created username and entered my password.
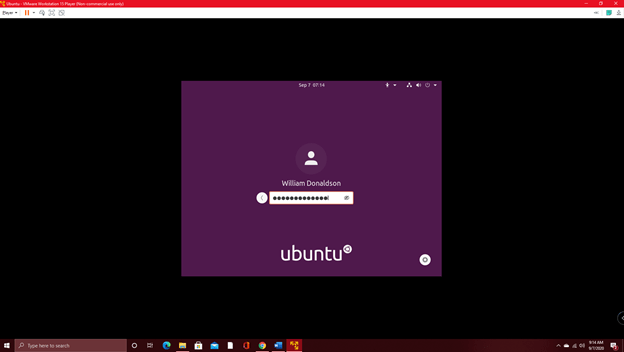
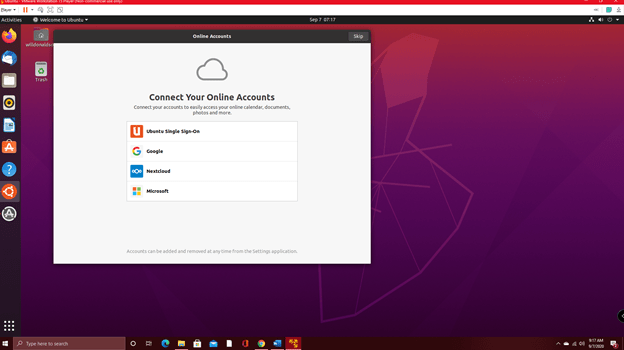
After successfully logging in, I was shown the below screen.
Overall, I felt that this assignment was a great learning experience for me as I have wanted to try Ubuntu/Linux for a long time. As a current IT manager, having access to different operating systems is an excellent tool for deploying products and services, testing and verifying threats in a secure environment, as well as being able to navigate the IoT efficiently.
I hope we utilize VMs often in this course as it is one skill I have yet to develop fully. While the assignment was merely to install the VM, I will undoubtedly continue to play around in Ubuntu today to familiarize myself with the system. My experience with Linux is somewhat lacking; while I used it for a few college assignments many years ago, as well as my familiarity with Android systems, I hope to expand my skill set in this course. I can’t think of a better method to learn more about cloud computing than by working with VMs.
References
Ubuntu. (n.d.). Ubuntu Desktop. Retrieved September 7, 2020, from https://ubuntu.com/download/desktop/thank-you?version=20.04.1&architecture=amd64.
What have you learned through this process?
This week, we are tasked with creating a VM environment and installing an OS. In the past, I have worked with VMs a little for school but never dedicated enough time to the technology to fully immerse myself. I decided to use VMware Workstation 15 Player to host my virtual environment, and since I have meant to try Linux for some time, I figured Ubuntu would be a great learning platform for beginners. The install was relatively simple until I ran into an error due to Intel VT not being enabled; a quick edit of some BIOS settings resolved this. As we will be later running multiple VMs, I am glad I just upgraded one of my PCs with 48GB of RAM.
What are the implications of this mini-hypervisor?
The greatest thing about using/having access to multiple OS’s through VMs is the sheer functionality available at your fingertips. Utilizing a hypervisor enables a user to use various OS’s on the same hardware, allowing someone to take advantage of each OS’ abilities. Having a software-based OS also allows you to physically boot into a separate OS during your computer’s boot sequence. Hypervisors have been known to be vulnerable to cyberattacks and such; however, with the right security settings and maintenance, a hypervisor opens up a world of possibilities for those who wish to test out new programs, open up malicious content in a secure environment (separate from your primary OS), as well as be able to effectively handle processes that require a different OS than the one a user is currently using.
What kind of administration/management would need to be in place to keep all these optimized?
To efficiently administer and manage multiple VMs and OS’s, there are specific tasks one needs to ensure are completed, including updating both the VM launcher and each OS that you are working on as soon as an update is available (within reason/after testing), managing user access (specifically restricting access to those who do not require it), and properly allocating system resources to ensure the performance of each VM (as well as the primary OS) are up to the task. For example, I know running multiple VM’s can require a hefty amount of RAM, so preparing for future VM growth is essential.
What kind of security?
As securing a single OS can be challenging to some, the possibility of encountering threats when running multiple VMs significantly grows. One of the most vital aspects of securing several VMs is merely monitoring the activity of each environment for suspicious or malicious content/access. Automation of security configurations can be achieved relatively simply; however, researching how to perform them is the tricky part. Administrators should set up access control systems and policies and enable alerts on any unauthorized access. As with all OS’s, utilizing virus and malware protection/scanners, as well as creating backups of your data, are always recommended.
Do you really need virtual machines to achieve cloud computing?
Since cloud computing in modern times is such a broad category, you do not necessarily need a VM to utilize the technology. Many of the programs and services we all use utilize cloud computing, such as Facebook, Google Drive, and Dropbox, where your data is stored on a remote machine, and much of the processing power isn’t derived from your PC. That being said, with the loose definitions of cloud computing, even Facebook could be considered a virtual machine of sorts, as it is an Internet-based tool to access a broad array of services and information (which operates somewhat separately from your own device).
Virtual machines are beneficial for running different operating systems; this enables those such as myself to dabble in a variety of valuable environments depending on the task at hand. As we all know, each variety of OS has its strengths and weaknesses; deciding upon the right tool for the job is half the battle in technology supremacy! I had a lot of fun with this week’s assignment. As I just built another PC using older parts I had lying around the office, I believe I will dedicate it to using Linux.
References
HyTrust. (2018, March 05). Protecting Your Hypervisor: When the Enemy Breaks Through the Line, Command and Control Is the New Soft Underbelly. Retrieved September 07, 2020, from https://www.hytrust.com/blog/protecting-your-hypervisor-when-the-enemy-breaks-through-the-line-command-and-control-is-the-new-soft-underbelly/
Sumastre, M. (2019, July 22). Virtualization 101: What is a Hypervisor? Retrieved September 07, 2020, from https://www.pluralsight.com/blog/it-ops/what-is-hypervisor
Ubuntu. (n.d.). Ubuntu Desktop. Retrieved September 7, 2020, from https://ubuntu.com/download/desktop/thank-you?version=20.04.1&architecture=amd64.
Categories: Software






