 Executive Summary
Executive Summary
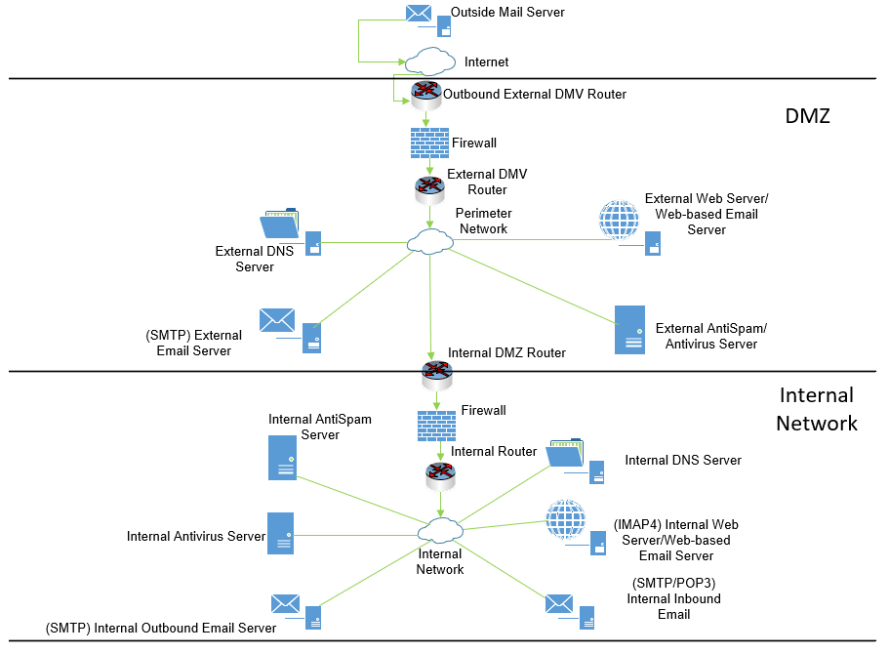
In this secure messaging infrastructure, we have each network separated into three general sections, an external-incoming Internet, DMZ, and the internal network. The system begins with an outside mail server utilizing SMTP to send email to the company (outside the company’s perimeter). Next, the Internet will connect all internal and DMV networks, secured by an outbound external DMZ router that routes traffic; the main drawback from this is that it only connects the perimeter network to the Internet. Next, unauthorized traffic (inbound/outbound) will be blocked by the firewall (to/from the perimeter network).
An external DMZ router will then route traffic into the perimeter network, then separates into five different paths, the internal DMZ router, external DNS server, external email server with SMTP, external web server for web-based email, and an external antispam and antimalware server. The external web server will utilize IMPA4 for outbound mail and messaging but doesn’t have the capability for inbound email. The external antivirus/antimalware server will protect the perimeter network from spam and viruses, but will not help the external network. The external DNS server will facilitate naming solutions for internal systems, but not the external network; furthermore, it will forward to the perimeter network DNS server for outside name resolution, which can cause issues. Next, the external email server will utilize SMTP to send outgoing emails, but not incoming.
The network will then travel from the DMZ to the internal system using the internal DMZ router, through the firewall, and to the internal router. From the internal router, the network is then split into various channels, such as the internal DNS server, internal web server for web-based email and messaging (utilizing IMAP4), SMTP/POP3-based internal inbound email server, SMTP-based internal outbound email server, internal antivirus server, and an internal antimalware server.
Using SMTP to send messages is quite flexible and easy to set up, however, the protocol itself can be insecure, as well as offers limitations regarding servers. Using IMAP4 and POP3 with SMTP would be efficient as synchronization would be simple, and migration would be straightforward; however, performance might suffer compared to other protocols (and maintenance can be troublesome).
References
Stallings, W. (2017). Network Security Essentials: Applications and Standards (Sixth). Pearson.
Categories: Security






